1984. Orwell still alive at present time.
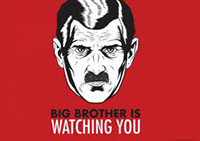
Workshop. December 2013. Published in 1949 George Orwell’s dystopian novel ‘1984’ depicts a world in the aftermath of a global atomic war which has eliminated nations, decimated populations and depleted most of the Earth’s resources, leaving those who have survived to become ‘slaves’ to Big Brother and the Party. The Party justifies their authoritarian rule as in the best interests of the people. To maintain order and protect national security The Party uses official deception, secret surveillance and constant censorship. All citizens are subjected to uninterrupted secret surveillance by The Party; hidden cameras, microphones and government informants are used surreptitiously to collect and record information of those inclined to criticize The Party.
The novel’s protagonist, Winston Smith, keeps a journal in which he criticizes Big Brother, The Party andits ideology, a capital offense according to The Party; the punishment – death. ‘1984’ portrays a world in which 85 percent of the population are poor and uneducated; The Party ensures they are kept that way by sedating them with alcohol, pornography and the National Lottery. Diversionary tactics used to divert the mass’ attention and to keep them from seeking the truth, secure The Party’s rule. Then, as now, all those who speak out strongly against the system are tracked, spied on and ultimately eliminated.
At the time of publication Orwell’s novel may have seemed a fantasy tale, a far-fetched exaggeration, skirting the borders of paranoia. Not so anymore. Our privacy, much like Winston’s, is being invaded by governments, the media, employers, businesses, criminals and others all over the world who use digital technologies to eavesdrop.
While Orwell has often been used as a standard point of reference in surveillance studies, other paradigms are equally being used. Michel Foucault’s panopticom metaphor is cited more often in the current cultural context as being the appropriate model for investigating surveillance studies. Yet both the Orwellian and Foucaultian paradigms are being questioned and debated as to their usefulness by surveillance studies scholars.
At the forefront of this theoretical turn in surveillance studies has been Kevin Haggerty and Richard Ericson’s article ‘The Surveillant Assemblage’ (2000). According to Haggerty and Ericson, Foucault’s panopticon improved upon Orwell’s Big Brother by reminding us that the proletariat have long been the subject of intense scrutiny and by situating surveillance in the context of a theory of power. Yet they argue that ‘rapid technological developments, particularly the rise of computerized databases, require us to rethink the panoptic metaphor’ (2000, p. 607).
They point out that in both Orwell and Foucault surveillance is a regime where the many watch the few in top-down scrutiny. In order to move away from Orwell and Foucault, they draw on Deleuze and Guattari’s notion of the ‘assemblage’ to produce what they call the ‘surveillant assemblage,’ which works by ‘abstracting human bodies from their territorial settings into discrete data flows that are later reassembled
into data doubles’ (200, p. 605).
Regardless of what we choose as the most fitting metaphor, the need to understand how and why surveillance is being used, requires investigation from a multiplicity of perspectives.
The bulk of research on privacy has traditionally been generated from the point of view of a single perspective held within specific academic disciplines. Seen as such privacy concerns become embedded within a particular domain, each claiming to be sole owner of the issues.
In today’s technologically oriented society investigating privacy from a unique perspective is not only illogical, it also seems nearly impossible. Any agreed upon course of action or regulations to address the issues, would be incomplete, limited in effectiveness. Privacy concerns cross disciplines, nation states, cultures and individuals worldwide in both the public and private sectors.
The increasing use of surveillance technology used to monitor, record and control the activities of all types of institutions and individuals, requires that we investigate privacy from an interdisciplinary point ofview.
Technology and its disruptive effects on a previously balanced social order, mandates renewed and thorough discussion on the uses and effects of such technology if we are to fully understand both the opportunities and threats presented by its use.
More information needs to be made available to the public so that the people become aware of how privacy concerns are related to them, how they can detect a potential invasion of privacy and what to do about it. People choose to give up personal information, people can choose to safeguard it.
Webster University Geneva’s fifth annual Media Trends Conference (April 3-4 2014) aims to assemble the top researchers, policy makers and privacy activists as we investigate the ambiguous terrain of technology and privacy interests.
In doing so, we have identified 6 areas that require urgent and critical analysis of privacy issues as related to surveillance and the ensuing regulatory attempts that are being drafted. Panels will focus on: whistleblowing, government and media collaboration, cybersecurity and cybercrime, media invasion of privacy, business and commercial interests and global regulatory developments.
Two workshops: 1) protecting yourself from cyber crime and 2) protecting freedom of speech, will be offered.
Keynote speakers have already been confirmed, including censored Swiss photographer, Christian Lutz.
The Media Trends Conference strongly encourages the submission of cross-disciplinary research and alternative points of view in order to promote debate and discussion on these often highly-contentious topic areas.
Interested parties are invited to submit abstracts until January 1st, 2014. Selected participants will be notified by January 15, 2014. Drafts of papers (meeting attached publishing guidelines) are due March 15, 2013. Submissions or info requests can sent to Tammy Rosso (rosso@webster.ch) and Rebekah Jorgensen (jorgensen@webster.ch) , or by post to the Dept. of Media Communications, Webster University Geneva, 15 route de Collex, 1293 Bellevue, Switzerland.
———————————————————————-
Perhaps the most transformative aspect of the Internet is its capability to foster networks of interaction that are distributed across almost infinite spans of space whilst also converging a range of different information technologies. Significant here is the fact that the networks generate multiple information flows which are also multi-directional, thus providing levels and types of connectivity not previously experienced by communications technologies. The Internet is not simply a super (Poster, 1995), virtual (Engberg, 1996) or electronic (Lyon, 1994: ch 4) Panopticon: an extension of Foucault’s conceptualisation of Bentham’s prison design – seeing without being seen (Foucault, 1983: 223), as has become the conventional wisdom. It is important to emphasise that Internet information flows are both panoptic and synoptic, because not only can the few watch the many, but the many can also watch the few (Mathieson, 1997: 215). The multi-directional informational flow helps to make the internet a distinctive surveillant assemblage (Haggerty and Ericson, 2000: 605) with an idolatrous dream of omniperception and a minacious twinkle in the electronic eye (Lyon, 2001a: 147). These processes can create enormous benefits for society, but the same processes also create opportunities for new and distinctive forms of criminal and harmful behaviours. Mapping out these behaviours to provide further understanding of cybercrimes will be the purpose of this chapter.